Every business venture involves uncertainty — especially for large organizations. A structured risk assessment process helps identify potential risks and roadblocks early, maintain team alignment, optimize resources, and keep objectives achievable. When threats go unnoticed, they can undermine even well-crafted plans.
Imagine your company preparing to enter global markets. You’ve developed a solid strategy, assigned necessary resources, and prepared your teams. However, overlooking potential regulatory changes or supply chain vulnerabilities could delay your launch, hurting both revenue and your brand’s reputation.
This article explores how thorough evaluation of potential threats helps organizations anticipate challenges, reduce disruptions, and maintain momentum. We’ll examine the essentials of threat identification, optimal timing, practical methodologies, and how a platform like monday work management can simplify this process across your organization.
What is risk assessment and why is it important?
The risk assessment process is a systematic approach for identifying, evaluating, and addressing uncertainties that might interfere with your business goals. Executives and assessors use this method to recognize obvious hazards, assess their potential impact, and develop strategies to mitigate possible disruptions.
This process serves 2 key purposes:
- Anticipatory planning: Identifying potential obstacles — like changing regulations or market instability — lets you develop contingency plans before problems emerge. Consider a bank expanding internationally that analyzes political stability factors months before market entry. Creating contingency plans early ensures expansion efforts remain on schedule despite unexpected challenges.
- Strategic opportunity evaluation: Setting clear boundaries on acceptable threats enables you to pursue growth while limiting exposure to unnecessary dangers. Establishing defined limits allows companies to take calculated chances without jeopardizing stability. For instance, when launching a new product, you might evaluate cybersecurity vulnerabilities early to avoid delays or damage to your company’s reputation.
By understanding emerging uncertainties, businesses can make better-informed decisions, optimize their assessment process, and develop strategies that align with long-term success.
The challenges with running a risk assessment
Despite the benefits, implementing a structured risk assessment process presents several challenges:
- Inconsistent information sources: Data gaps or unreliable inputs can skew your evaluation of potential outcomes and lead to flawed decisions.
- Expertise gaps: Complex assessments often require specialized assessors or additional staff training, increasing operational costs and potentially straining budgets.
- Organizational resistance: Teams may hesitate to adopt new processes, causing inefficiencies and delays.
- Speed versus depth tradeoffs: Finding the right balance between thorough evaluations and agile decision-making can be difficult.
Beyond internal factors, businesses must also evaluate operational hazards, legal compliance, and emergency preparedness to prevent disruptions.
Compliance roadblocks when assessing risk
Enterprises operating globally must regularly assess compliance with complex regulatory frameworks, such as the General Data Protection Regulation (GDPR) in the European Union (EU), Sarbanes-Oxley (SOX) for financial transparency in the U.S., and ISO standards for operational quality management. For instance, a multinational healthcare company regularly assesses GDPR compliance, safeguarding patient privacy, avoiding substantial fines, and protecting brand trust.
Compliance demands are continuously evolving. According to PwC’s October 2024 Pulse Survey, 75% of executives ranked cyber threats as a top business risk and anticipate tighter regulation and increased litigation in 2025. This highlights the importance of having a dedicated executive — like a Chief Risk Officer (CRO) — who ensures the organization remains ahead of regulatory shifts and litigation risks.
Essential questions your risk assessment should answer
A strong risk assessment process provides clarity by addressing key questions, including:
- What emerging challenges might affect our critical initiatives?
- How could these threats evolve, and what potential consequences might follow?
- What level of exposure is acceptable for different projects?
- Are we actively preventing issues or primarily reacting to them?
By addressing these questions early, businesses can confidently navigate uncertainty, align decisions with acceptable levels of exposure, and minimize unforeseen disruptions.
Pro tip: want to have AI find and assess all your risks for you? Check out our guide to AI-powered risk management.
Clarifying risk terminology: Assessment, management, and analysis
Though often confused, these terms represent distinct aspects of your organization’s approach to uncertainty:
- Risk management covers the ongoing process of identifying, evaluating, addressing, and monitoring potential dangers across your organization to protect long-term objectives.
- Risk assessment specifically identifies and evaluates particular vulnerabilities or hazards that could threaten specific business initiatives, providing critical insights to prioritize your responses.
- Risk analysis interprets your assessment results, highlighting which exposures require immediate attention and the most effective mitigation strategies.
For example, when implementing new enterprise software, you need all 3 elements. Risk management refers to the continuous oversight throughout the entire implementation process. Risk assessment pinpoints specific vulnerabilities, such as regulatory compliance gaps or cybersecurity liabilities. Risk analysis determines which issues are most urgent, guiding your team toward targeted actions that protect your timeline and objectives.
When to evaluate potential risks
Regular evaluations help you be proactive rather than reactive. You should assess potential threats at the following times:
- Before launching major initiatives: New projects, major investments (such as infrastructure, technology upgrades, or R&D), or strategic partnerships or mergers.
- During significant transitions: Acquisitions and market expansions, regulatory or compliance changes, technology upgrades or system migrations, and leadership or organizational changes.
- Throughout normal operations: Consistent reviews identify emerging issues before they grow serious
If your company is migrating from on-premise servers to cloud infrastructure, early assessment allows technical and compliance teams to preemptively address cybersecurity exposures or compliance challenges, ensuring a seamless transition without regulatory friction.
5 types of risk assessments for enterprises
Choosing the right risk assessment method depends on your industry, risk profile, and available data. Below are the 5 most common approaches.
1. Quantitative risk assessment
Best for: Data-rich situations where precision directly impacts your bottom line
This approach assigns specific dollar values to threats, giving you clear financial measures of what’s at stake. JPMorgan Chase uses this method to forecast potential liquidity and credit issues — enabling quick strategy shifts during market turbulence like we saw in 2020.
Keep in mind: You’ll need experts and solid data, which can get expensive.
2. Qualitative risk assessment
Best for: When you need quick insights or lack hard data
This method relies on your team’s experience and industry knowledge to categorize threats simply as high, medium, or low priority. For instance, software companies regularly consult project managers and support teams to identify potential integration hazards early — before customers feel any impact.
Keep in mind: It’s quick and easy, but opinions can vary, so involve multiple perspectives.
3. Semi-quantitative risk assessment
Best for: When you need both thoughtful analysis and quick decisions
This middle-ground approach combines qualitative judgments with simple numerical scoring (like 1–5 ratings), helping you prioritize without complex financial models. Healthcare organizations often use this method to quickly rank data privacy concerns based on patient impact and how likely they are to occur.
Keep in mind: You’ll still rely on judgment, so clearly define your scoring system.
4. Site-specific risk assessment
Best for: When you’re expanding into new regions or operating across diverse environments
These evaluations focus on challenges unique to particular sites. When Ford expanded globally, this approach helped them tackle region-specific challenges like local regulations, worker safety requirements, and operational needs.
Keep in mind: You’ll need local insights, so consider bringing in regional experts.
5. Dynamic risk assessment
Best for: Crises and fast-changing scenarios that demand immediate action
This approach provides immediate guidance during rapidly changing situations. During supply chain disruptions caused by political unrest, Pfizer quickly evaluated alternatives and adapted their sourcing strategy, keeping critical medications flowing.
Keep in mind: You’ll need agile teams ready to act fast. Slow decisions can hurt your response.
How to conduct a risk assessment in 6 steps
A successful approach should be clear, structured, and ongoing. Follow these steps to handle uncertainty while pursuing your goals:
1. Spot potential problems early
Identify vulnerabilities across your operation — from strategy to finance to security. When expanding globally, you might flag currency fluctuations, regulatory changes, or political instability as possible challenges.
2. Measure potential impact and likelihood
For each identified issue, consider:
- Impact: How severe would the consequences be if this issue occurs (e.g., financial loss, reputational harm)?
- Likelihood: Within your assessment period (e.g., the duration of your project, fiscal year, or strategic planning window), how probable is it that this issue will actually happen?
A simple risk matrix helps visualize and prioritize these factors clearly.
How to use a risk matrix
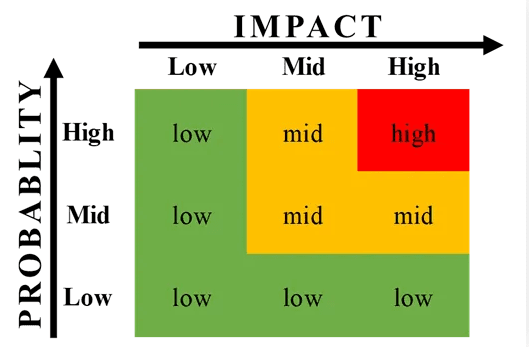
To implement effectively:
- Define what “impact” means: Create clear descriptions for minor through critical impacts.
- Establish likelihood categories: Set clear thresholds (e.g., likely, possible, unlikely).
- Plot each vulnerability: Place issues on the matrix based on your assessment.
- Focus on what matters most: Address high-severity issues that threaten key goals first.
- Watch for changes: Track how threats shift as you implement solutions.
3. Choose your response strategy
These four strategies are recommended by leading organizations like the Project Management Institute (PMI). They’re widely used because they’re simple, clear, and effective.
Here’s a quick breakdown of each with practical examples:
- Avoid: Completely remove the issue by adjusting your plans — like skipping an unstable market.
- Reduce: Lower the chance or impact — such as conducting cybersecurity training to prevent breaches.
- Share: Distribute responsibility, for example, by using cloud providers like AWS for data security.
- Accept: Acknowledge minor issues without immediate action, like allowing minor currency fluctuations that won’t hurt profits.
4. Assign ownership and action plans
Make specific people accountable for addressing each significant risk. When facing data privacy concerns, making your Chief Information Security Officer (CISO) directly responsible ensures proper oversight and timely action.
5. Implement continuous monitoring
Set up risk tracking systems to monitor high-priority issues in real time. During critical product launches, consider weekly updates with automated alerts for significant developments.
Ask yourself: How often does your team revisit risk assessments after creating them?
6. Learn from experience
After completing major projects, analyze what happened to improve future evaluations:
- Which predicted problems actually occurred?
- How accurate were your initial assessments?
- What could make your next evaluation more effective?
This ongoing improvement transforms enterprise risk management from a compliance checkbox into a real competitive advantage.
Real-world examples of managing risk at scale
Systematic evaluations help safeguard your business strategy, reputation, and finances. Here’s how companies turned potential disasters into positive risks or opportunities for improvement:
IT & cybersecurity
Cybersecurity threats remain a significant challenge for enterprises. In fact, according to Forrester, 78% of organizations reported experiencing at least 1 data breach in the past year, with 22% experiencing between 6 and 10 breaches.
Consider Equifax, which faced one of history’s most severe breaches in 2017. It affected 147 million people and resulted in over $700 million in losses. This crisis forced them to completely transform their approach to security by:
- Implementing comprehensive vulnerability scanning
- Deploying advanced threat detection technology
- Establishing continuous employee security training
Key takeaways: Start with a security audit that identifies your most sensitive data assets. Then build protective measures that match your specific vulnerabilities — not just generic best practices.
Financial risk management
When COVID-19 hit, JP Morgan Chase was ready. Their consistent use of data-driven risk modeling helped them:
- Anticipate liquidity challenges before they occurred
- Adjust market positions quickly as conditions changed
- Maintain stability despite unprecedented economic turbulence
Key takeaways: Create financial stress tests for your business that model various scenarios — from mild downturns to severe disruptions. Then develop specific action plans for each potential situation.
Supply chain risks
The 2011 Tōhoku earthquake and tsunami taught Toyota a painful lesson about supplier vulnerability. In response, they:
- Mapped their entire supplier network to identify dependencies
- Built relationships with alternative suppliers in different regions
- Created inventory buffers for critical components
This preparation paid off during the 2021 semiconductor shortage when Toyota maintained production better than competitors who lacked backup plans.
Key takeaways: Identify single points of failure in your supply chain and develop backup sources for critical materials or services.
Project management
IBM’s enterprise software rollout for Melbourne Water demonstrates how structured risk assessment ensures complex initiatives stay on track:
- Regularly assessed potential integration and compatibility issues ahead of software deployment
- Quickly flagged budget variances using unified monitoring dashboards
- Assigned clear risk ownership to senior project leads for rapid issue resolution
Key takeaways: Assign clear ownership to specific leaders who can swiftly address emerging issues — ensuring your enterprise maintains timelines, controls costs, and keeps clients satisfied.
Practical ways to streamline your approach to risk
Managing threats effectively requires both structure and flexibility. Here are practical ways to build threat prevention into your everyday operations:
Align risk management with your business goals
Integrate your threat assessment directly into strategic planning — don’t isolate it as just another compliance activity. Clearly show how each identified issue relates to specific business objectives.
Try this: Use a simple table to connect each identified vulnerability to the business goal it might impact. This makes the connection easy for everyone to understand.
Standardize workflows for consistency
Use standardized methods across your organization to ensure everyone evaluates threats using the same criteria.
Try this: Implement a basic risk register using the project risk register template that tracks:
- Description of potential issue
- Impact rating
- Likelihood rating
- Person responsible for addressing it
- Current status and next steps
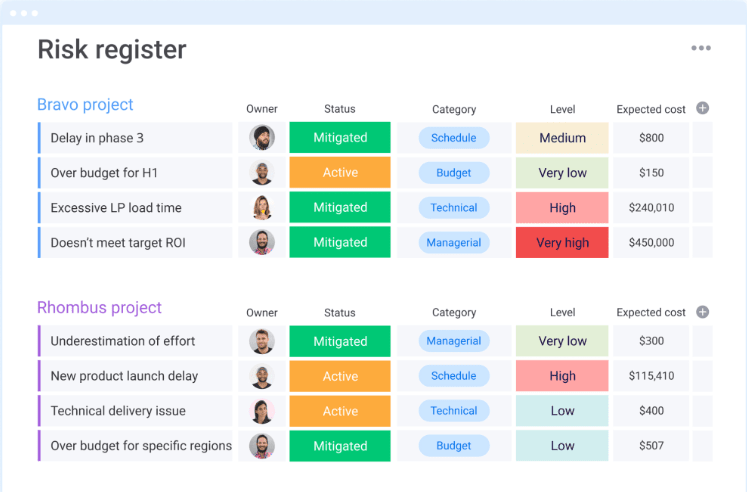
Want to learn more about a risk register? Read about what a risk register is and how it works.
Set up early warning systems
Move from reacting to problems to preventing them by creating automated alerts for emerging threats.
Try this: Configure alerts for key indicators such as unusual transactions, new regulations impacting your industry, or delays from critical suppliers.
Get a complete view of your threat landscape
Use centralized dashboards to see threats across different departments and locations.
Try this: Create a visual heat map showing your highest-priority concerns across the organization, updated in real time as conditions change.
Implementing these practical approaches helps align your threat prevention with business priorities, reduces uncertainty, and builds resilience that supports long-term growth.
How monday work management powers enterprise risk assessment
Managing potential problems effectively requires more than just good planning; you need a system built for complex organizations dealing with diverse uncertainties.
With monday work management, you can integrate threat prevention directly into your planning process, giving you early insight into challenges before they affect your business goals. This visibility helps you plan responses and stay nimble when conditions change.
Turn potential threats into clear actions
Your teams tackle uncertainty best when they have clear objectives and responsibilities.
With monday work management, you can easily:
- Document and track vulnerabilities in one intuitive workspace
- Assign accountability for risk mitigation efforts
- Track progress and ensure timely follow-through
For example: A pharmaceutical company might track regulatory issues by region, assign compliance specialists to address each requirement, and give executives real-time progress updates — keeping approvals on schedule and operations running smoothly.
Monitor issues across your entire organization
When you operate in multiple locations or departments, you need a comprehensive view of potential problems. Interactive dashboards provide instant insight into threat levels across your entire organization.
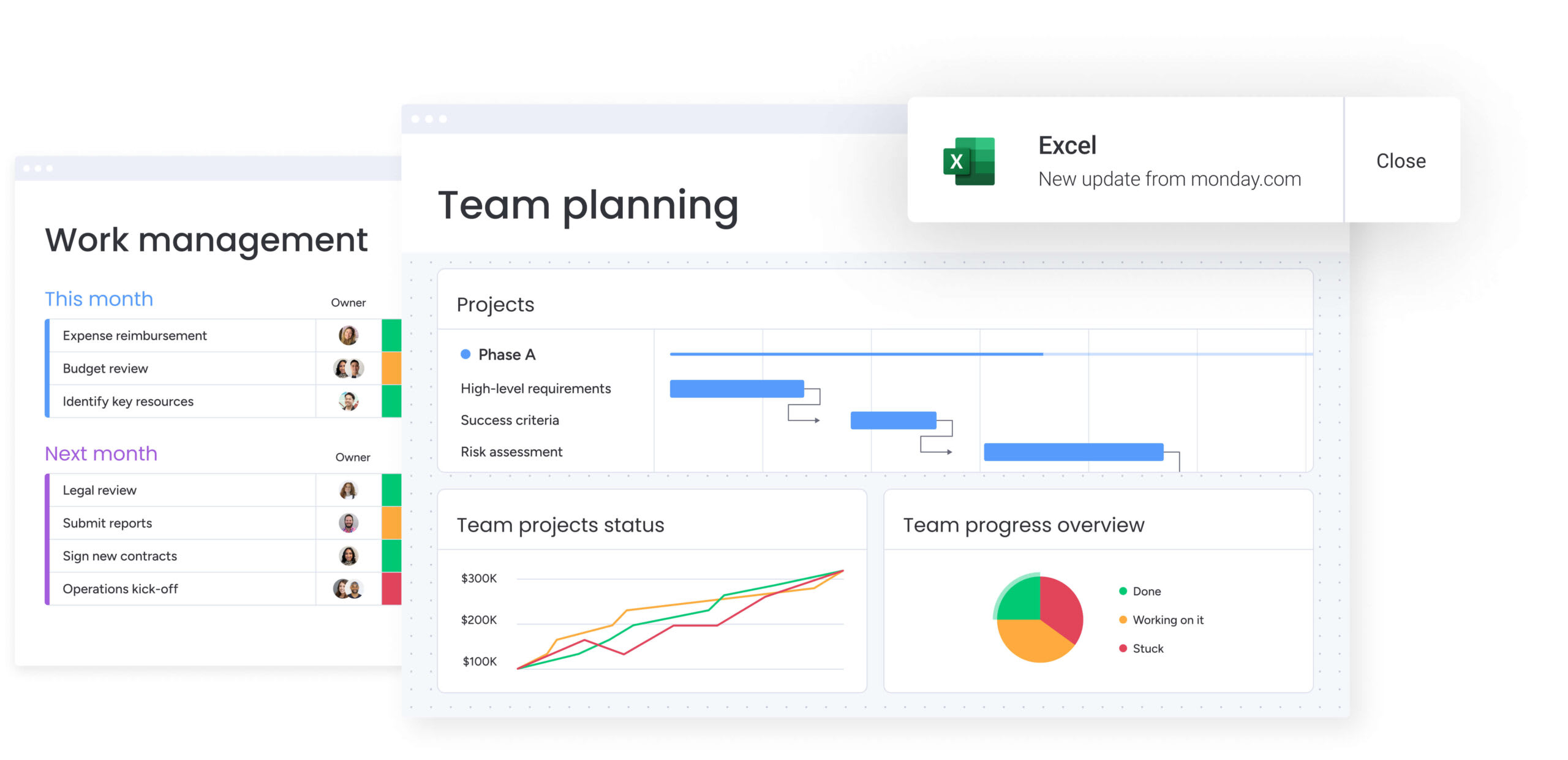
Real-world application: Your IT security team spots unusual activity across several regional offices. Color-coded visuals immediately highlight the highest-risk locations, letting you respond quickly and prevent a potential data breach.
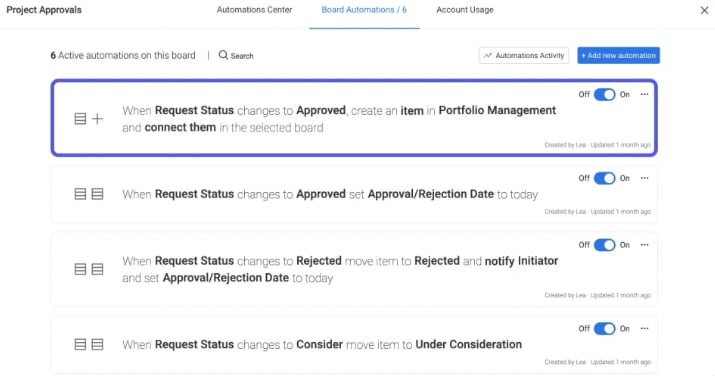
Automate key parts of your process
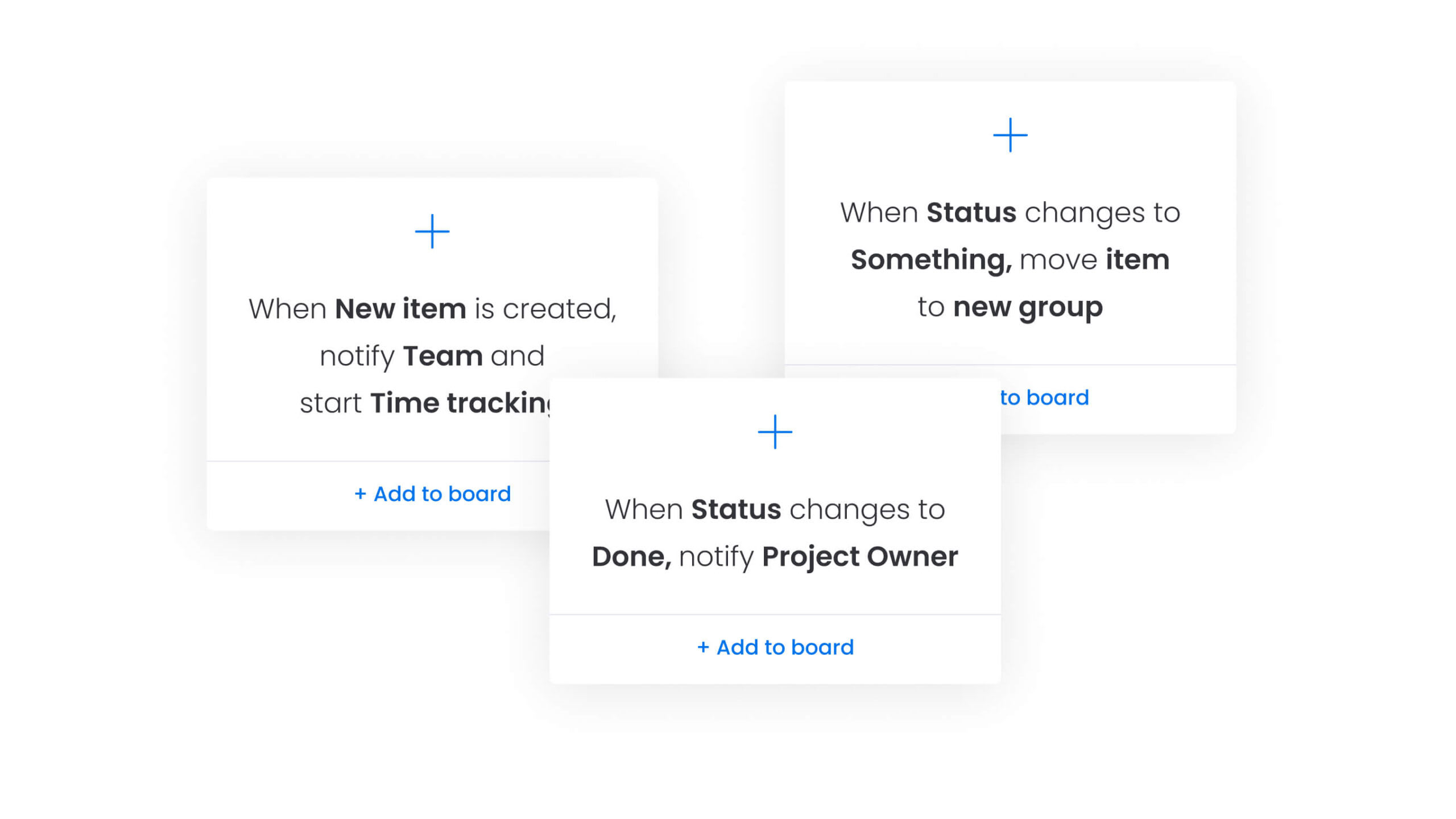
As your organization grows, threat management becomes more complex. Automation helps by:
- Flagging high-priority issues for immediate attention
- Moving approvals forward without unnecessary delays
- Eliminating process bottlenecks
How it works in practice: Your finance team sets up alerts triggered by specific market changes. When conditions shift, your team receives automatic notifications to adjust investment strategies — protecting your financial position without constant manual monitoring.
Make better decisions with smart risk management
Effective risk assessment helps protect your strategies and keeps your business moving forward. With the right tools, your organization can anticipate and avoid costly disruptions, turning potential obstacles into real opportunities.
A platform like monday work management provides clear oversight, streamlined workflows, and focused accountability, so your teams can address threats early and confidently grow the business.
Try monday work management and turn proactive risk management into your competitive advantage.
FAQs
What are the 5 main steps of risk assessment?
Risk assessment follows 5 key steps:
- Identify potential hazards: Recognize possible threats in the environment.
- Assess risks: Evaluate impact and likelihood.
- Determine controls: Establish mitigation measures.
- Document findings: Record risks and response plans.
- Review and update: Continuously refine strategies.
What are the 5 Cs of risk assessment?
The 5 Cs help structure an effective risk assessment:
- Context: Understand the business environment and external factors.
- Criteria: Define acceptable risk thresholds.
- Consequences: Evaluate the potential impact of risks.
- Control: Identify measures to mitigate or prevent risks.
- Communication: Keep stakeholders informed throughout the process.
- Criteria: Define acceptable risk thresholds.
What are some examples of risk assessments?
Risk assessments vary by industry and function. A cybersecurity risk assessment might analyze network vulnerabilities, while a financial risk assessment evaluates market fluctuations. In supply chain management, risk assessments identify potential disruptions, and enterprise project risk assessments ensure that major initiatives stay on track.
What are the components of risk assessment?
A complete risk assessment includes 4 core components:
- Hazard identification: Recognizing threats and uncertainties.
- Risk analysis: Measuring severity and probability.
- Risk evaluation: Prioritizing risks based on business impact.
- Risk control measures: Implementing strategies to mitigate risks.
- Risk analysis: Measuring severity and probability.
What is the goal of a risk assessment?
The primary goal of risk assessment is to help organizations identify potential threats, evaluate their impact, and implement strategies to minimize disruptions. This process supports business continuity, regulatory compliance, and long-term growth.
What are the 5 types of risk assessments?
Organizations use different types of risk assessments depending on their needs. Here are the 5 types:
- Qualitative risk assessment: Expert-driven, scenario-based analysis.
- Quantitative risk assessment: Uses data models to calculate risk probability.
- Semi-quantitative risk assessment: Blends expert judgment with scoring systems for prioritization.
- Site-specific risk assessment: Focuses on location-based hazards.
- Dynamic risk assessment: Adapts to real-time threats.
- Quantitative risk assessment: Uses data models to calculate risk probability.
What are the 4 main sections of a risk assessment?
Every risk assessment includes:
- Hazard identification: What potential threats exist?
- Risk analysis: How severe and likely are the risks?
- Risk evaluation: Which risks need immediate action?
- Risk control measures: What mitigation strategies are in place?
What are the 4 layers of risk assessment?
Risk assessments operate in 4 layers:
- Strategic risk assessment: Aligns risk management with long-term business objectives.
- Tactical risk assessment: Focuses on department and team-level risks.
- Operational risk assessment: Manages risks in daily business activities.
- Dynamic risk assessment: Assesses risks in real time for immediate action.
- Tactical risk assessment: Focuses on department and team-level risks.
- Tags:
- Project risk management
